Introduction
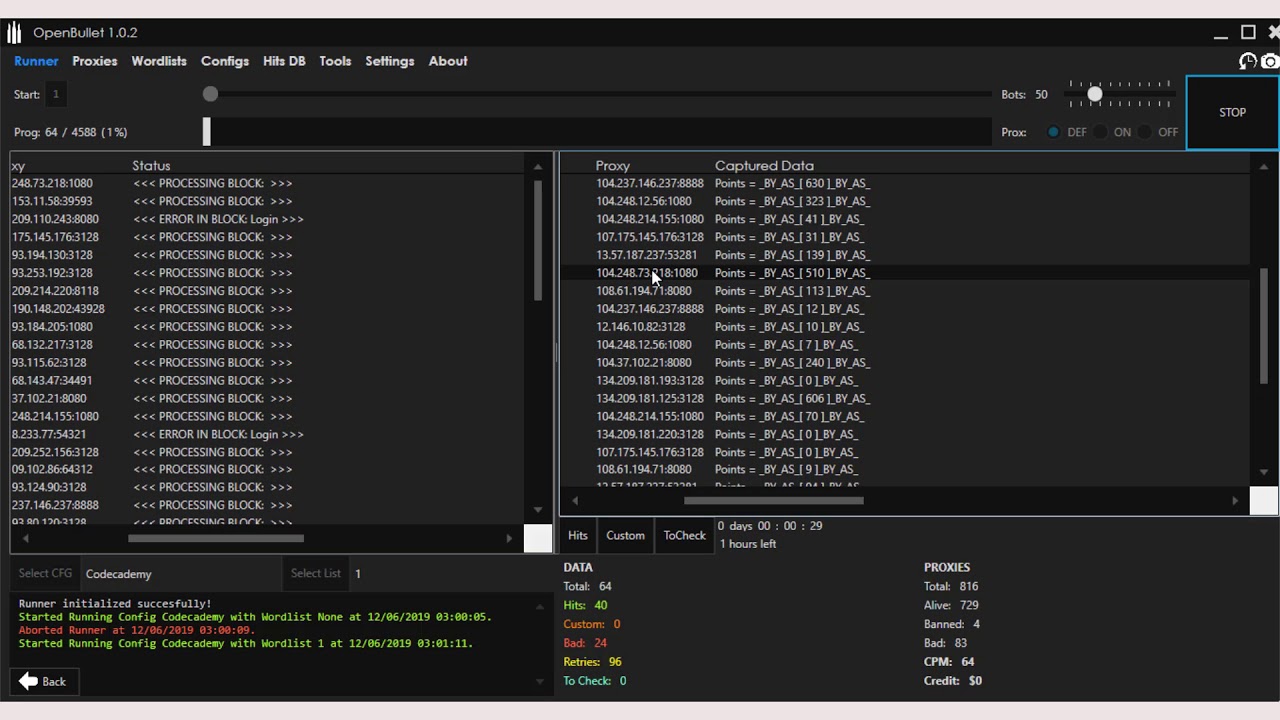
OpenBullet Anomaly is a powerful automated testing tool and web scraping suite that allows you to perform requests towards a target webapp and offers a lot of tools to work with the results. This software can be used for scraping and parsing data, automated pentesting, unit testing through selenium automation and much more. Download OpenBullet and SilverBullet configs for free from our store.