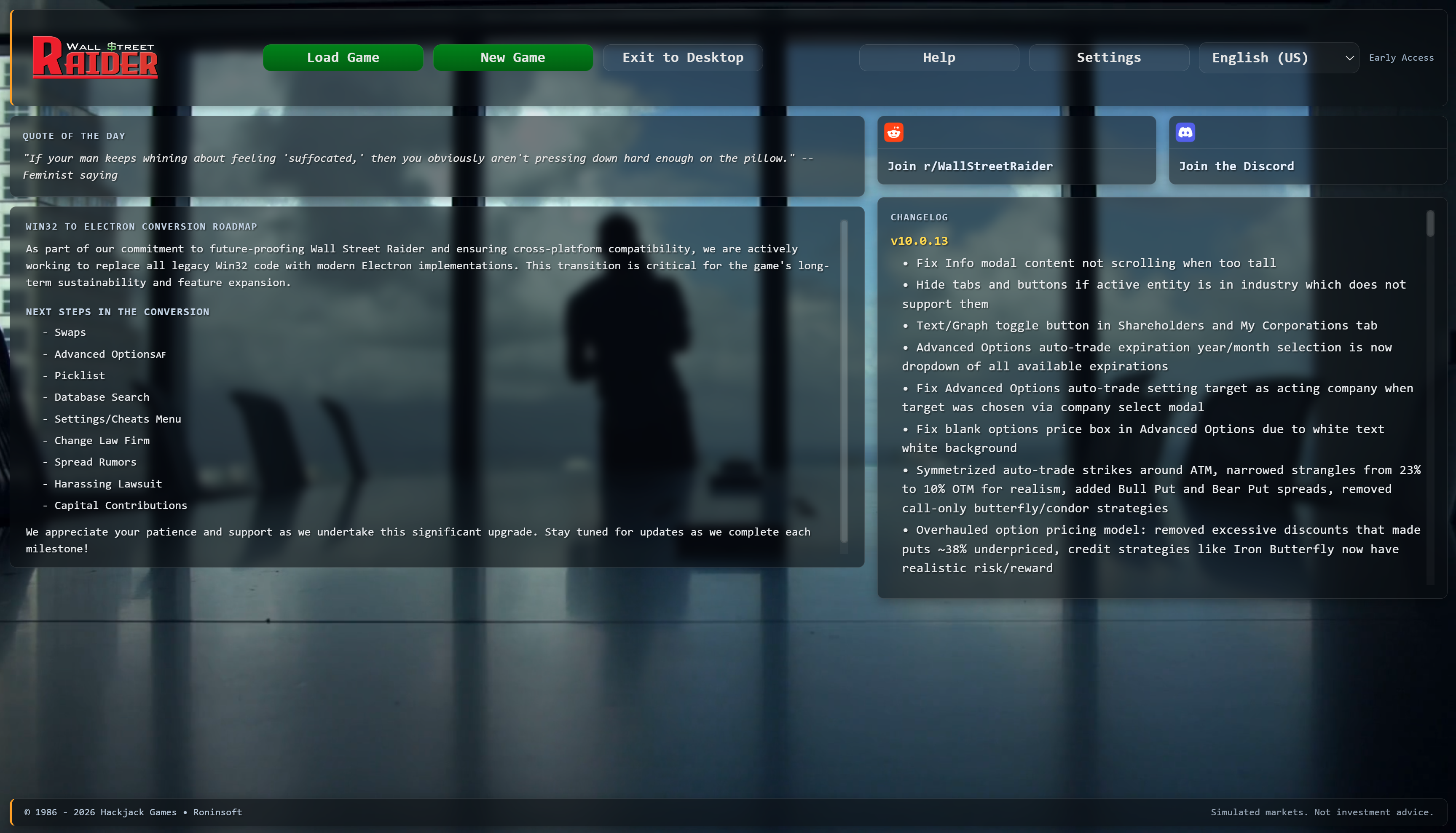
Since 1986 • 40 years of continuous development
Product Key And Serial Number Of Handycafe Apr 2026
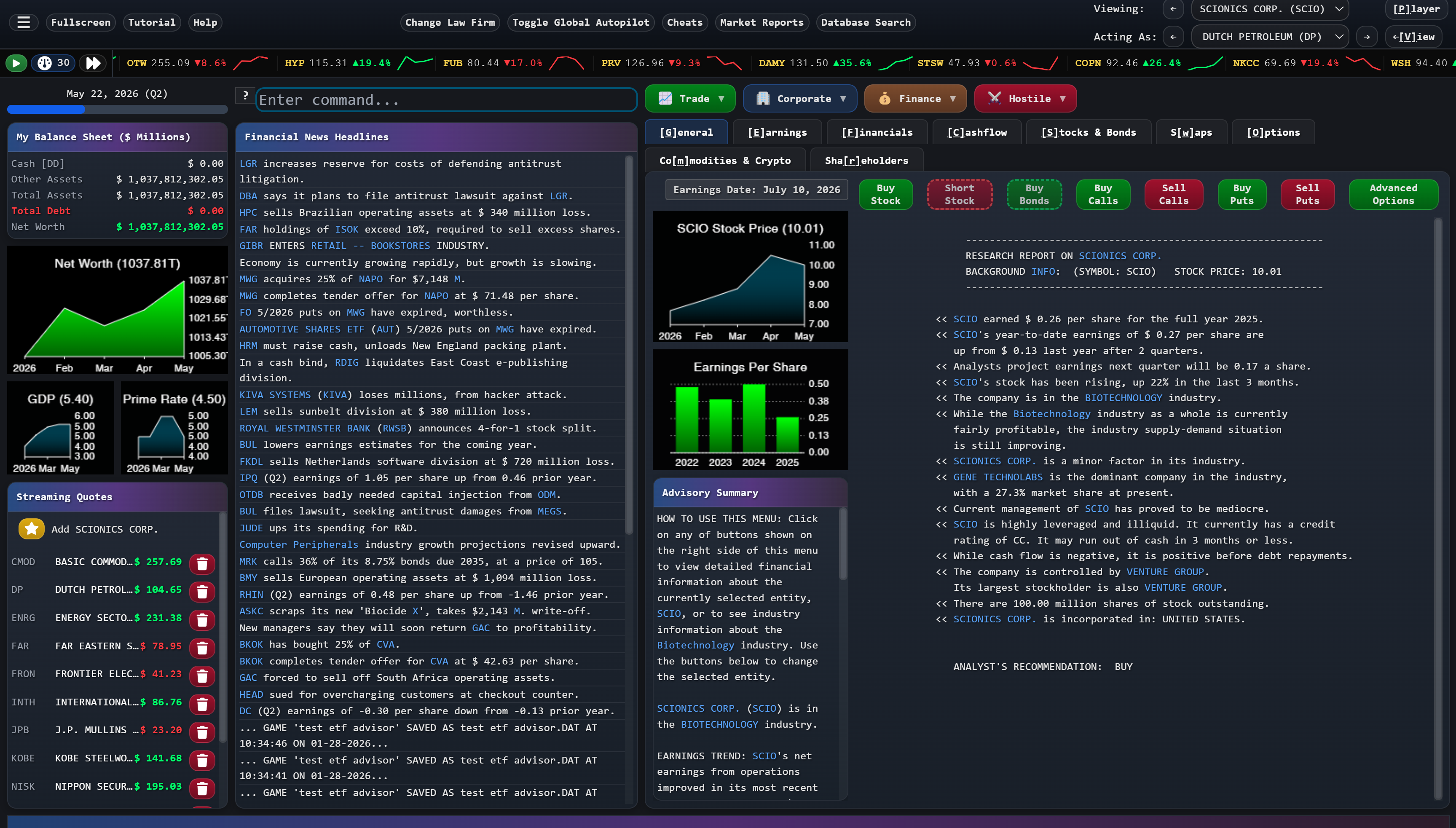
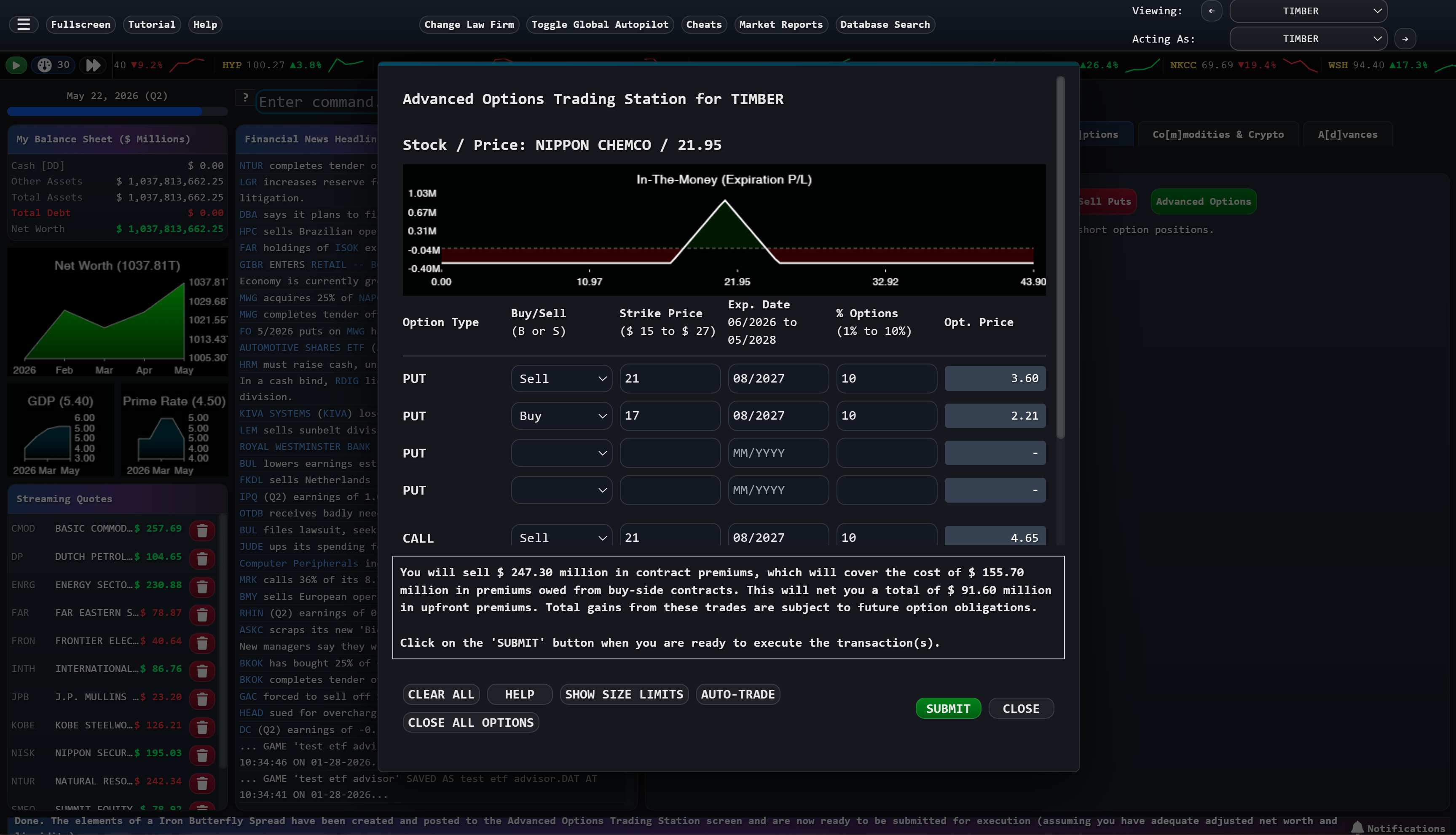
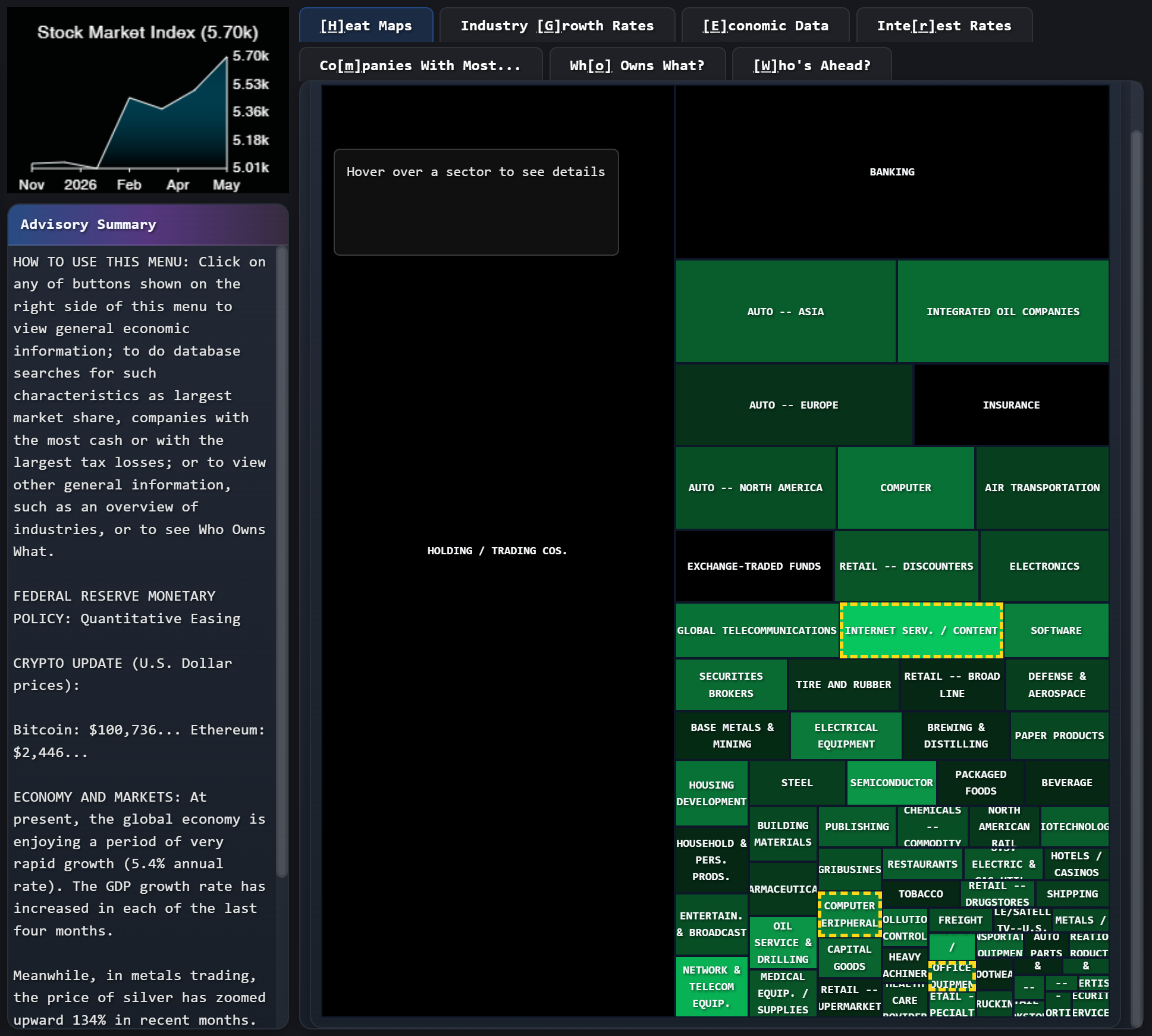
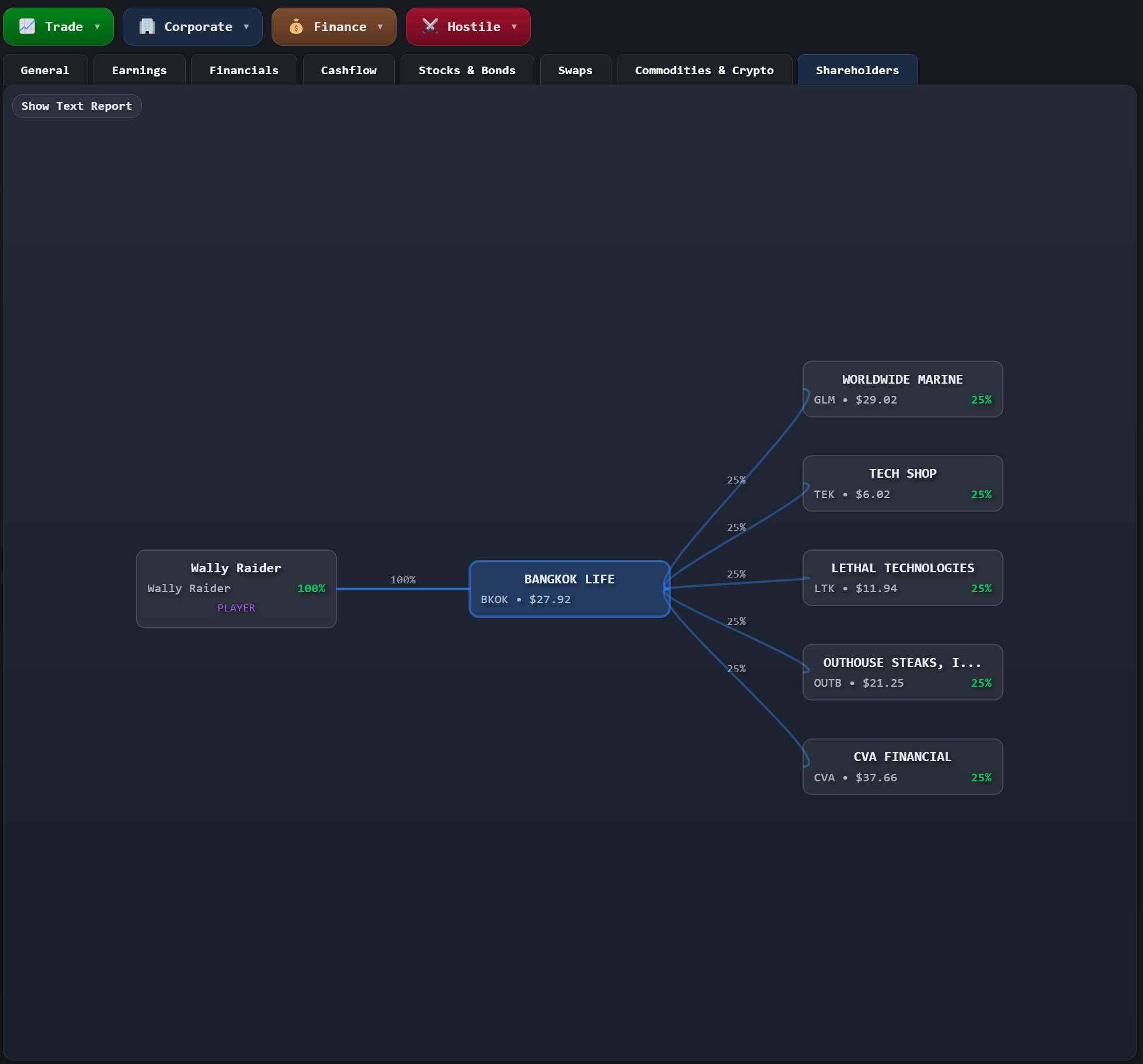
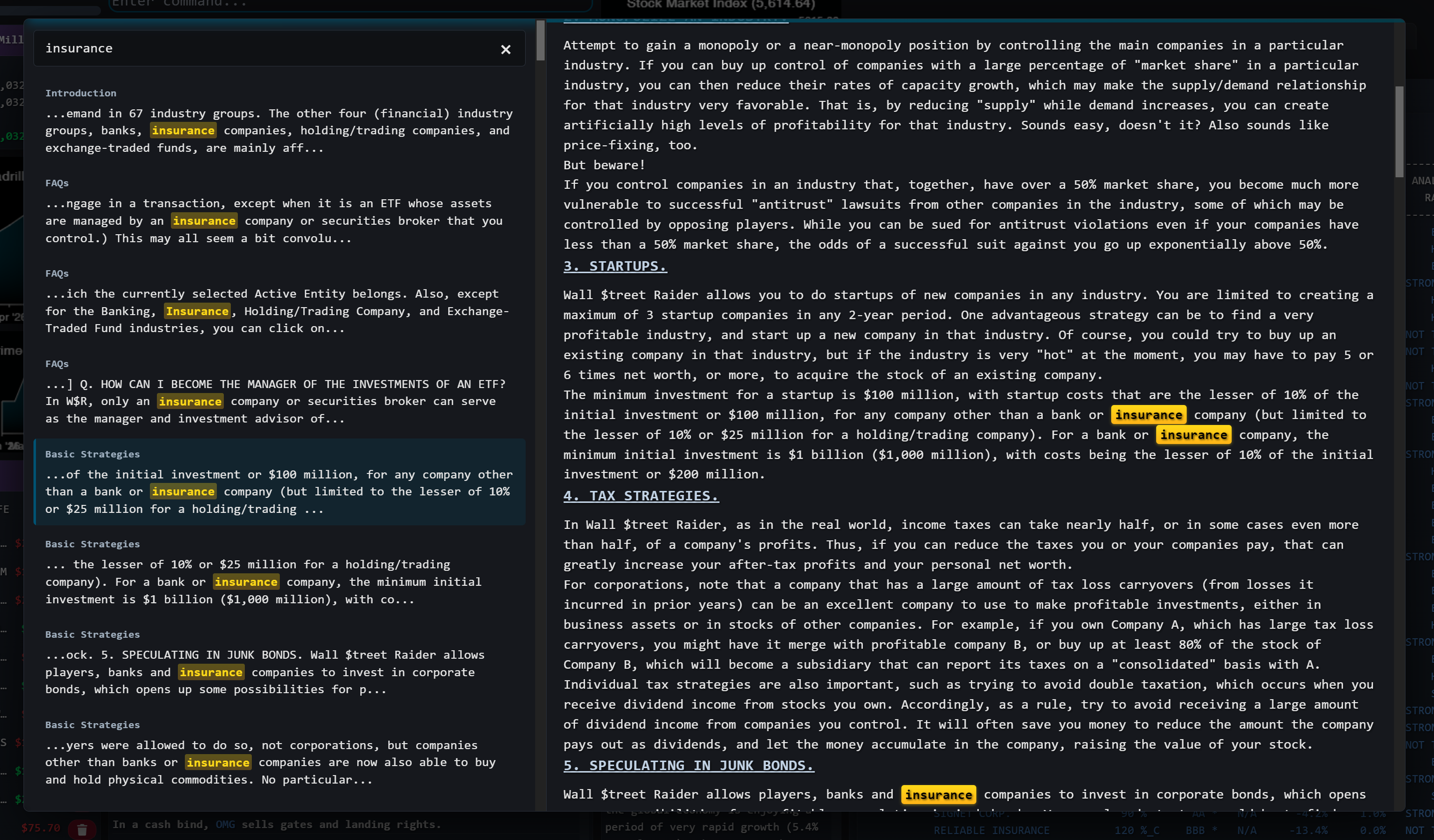
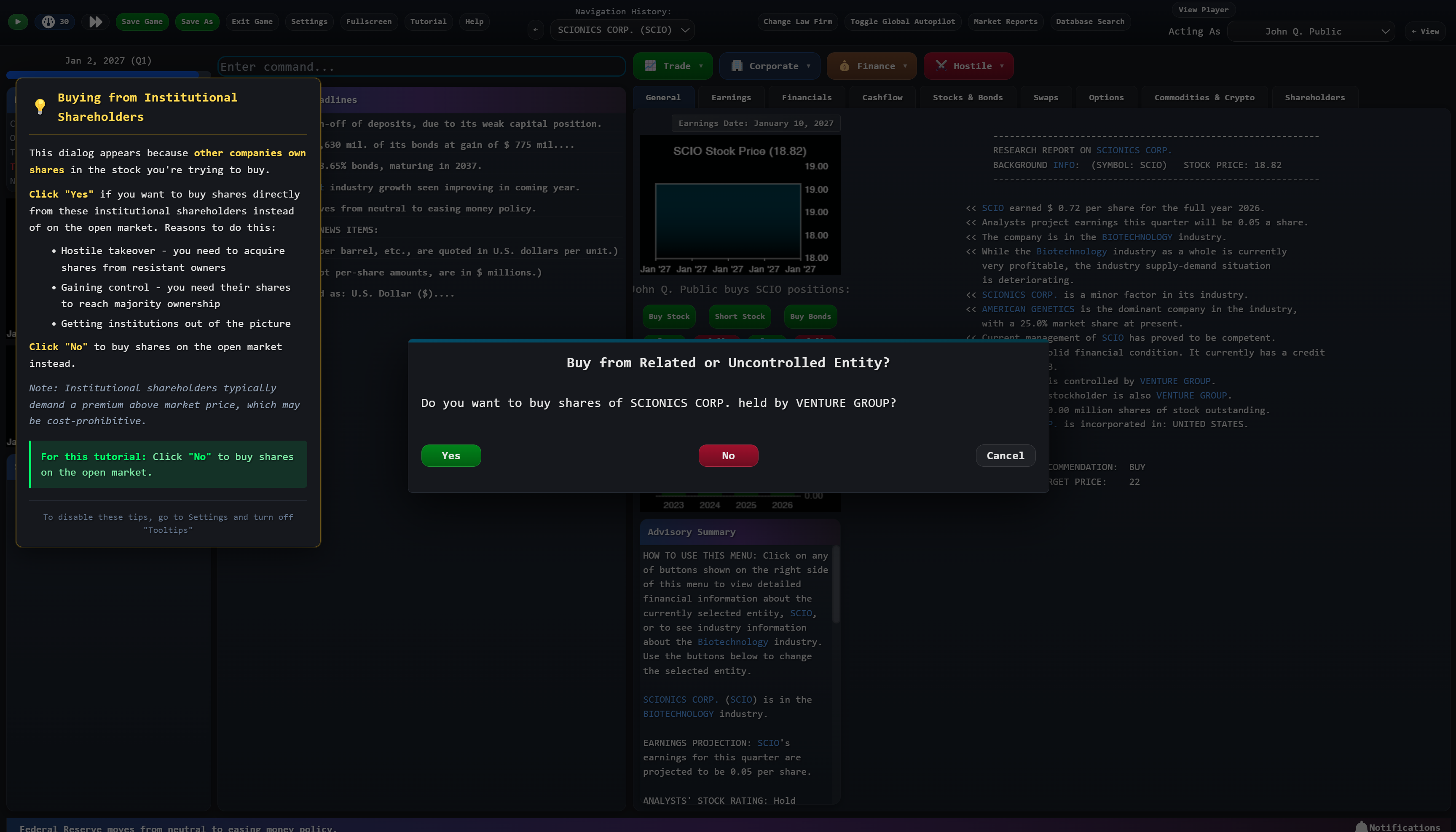
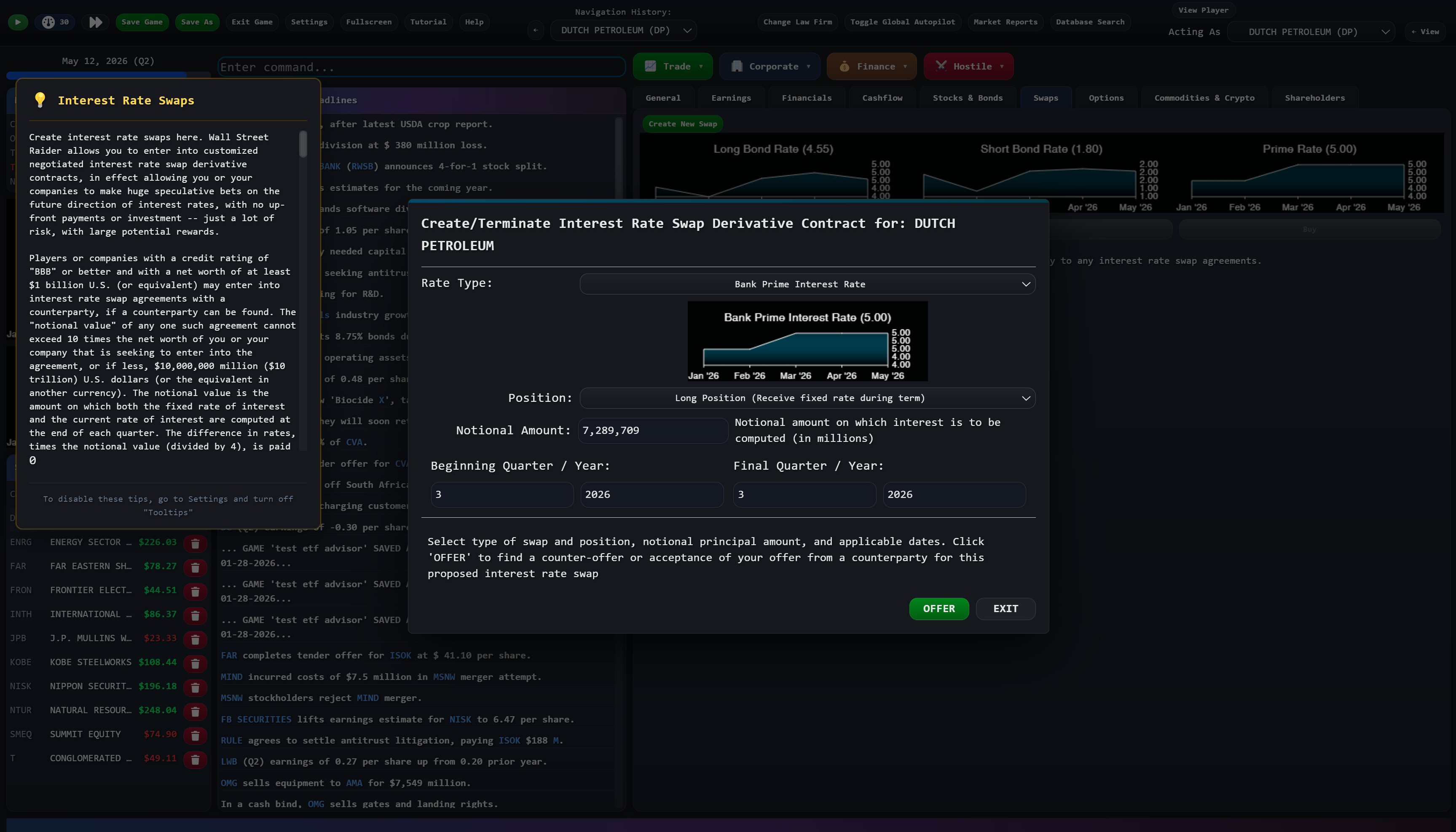
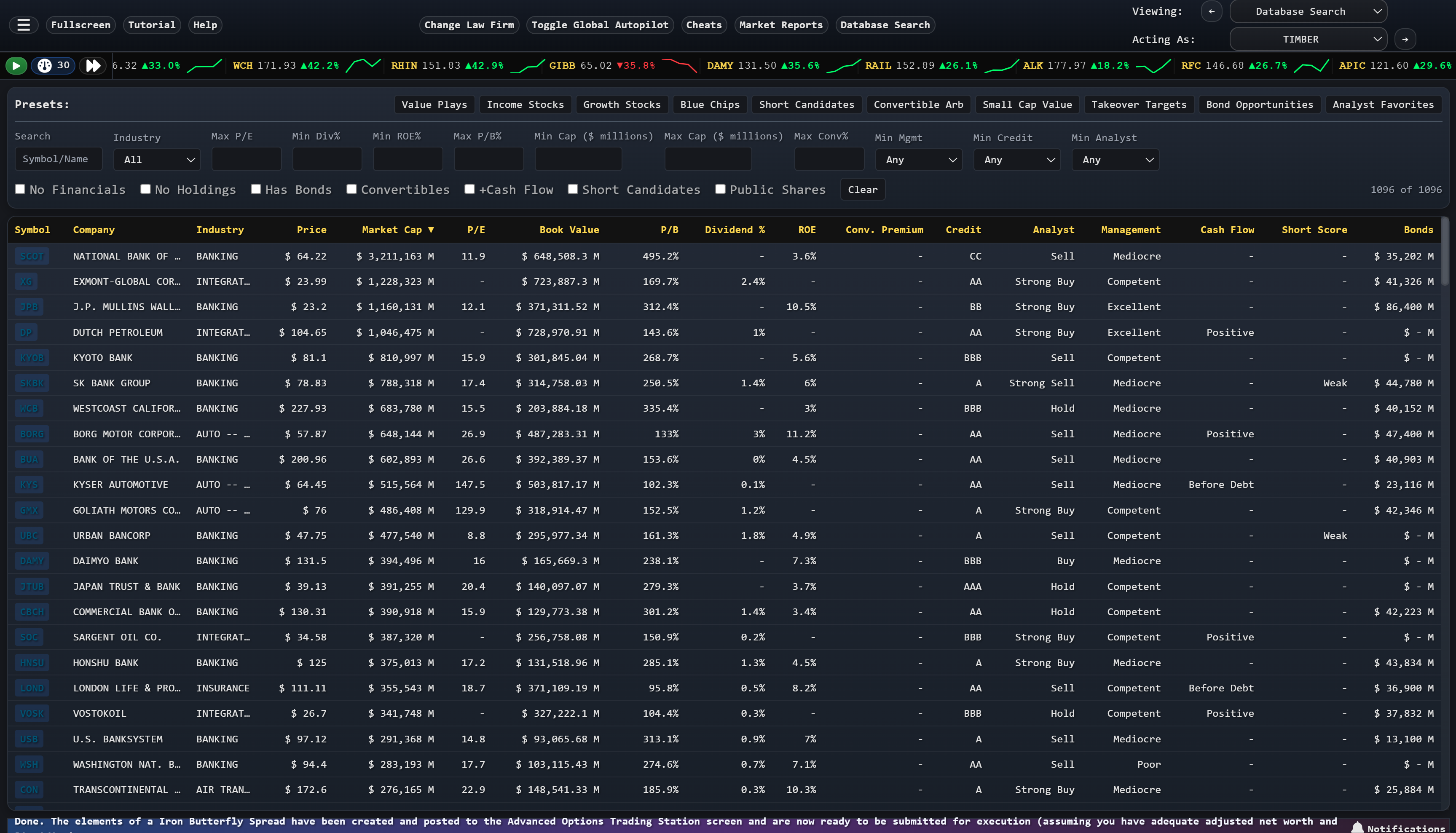
The most comprehensive financial simulation ever made. Trade stocks, bonds, options, futures, and more across 1,600 simulated companies. Now remastered for Steam.