V1.0 - Psn Liberator
If you own a PS3 today, stick to official firmware. The nostalgia isn’t worth the ban—or the risk to your account.
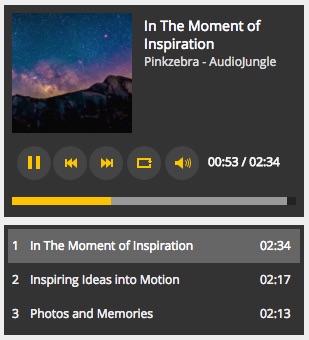
Today, PSN Liberator v1.0 exists only as a relic—a piece of digital history discussed in archived forums and YouTube retrospectives. It serves as a case study in why console makers moved to more robust, hardware-based security (e.g., PS4’s hypervisor and PS5’s AMD Trusted Execution Environment). PSN Liberator v1.0 was a bold, clever, and ultimately short-lived exploit. For a brief window, it gave homebrew enthusiasts and pirates alike the keys to the PlayStation kingdom. But like all such tools, it was a temporary victory—a single move in the endless chess game between hackers and hardware giants. psn liberator v1.0
In the early 2010s, the PlayStation 3 hacking scene was a battleground of cat-and-mouse security exploits. At the center of this storm emerged a tool called PSN Liberator v1.0 —a name that promised freedom but delivered a firestorm of controversy. What Was PSN Liberator v1.0? PSN Liberator v1.0 was not a game, a mod, or a simple cheat device. It was a proxy-based workaround designed to bypass Sony’s firmware version checks. In simple terms, it tricked the PlayStation Network (PSN) into allowing modified or jailbroken PS3 consoles to go online. If you own a PS3 today, stick to official firmware